Grant AWS Lambda Access to S3 Bucket or CloudWatch Logs
Last updated: Feb 26, 2024
Reading time·5 min

# Table of Contents
# Grant AWS Lambda Access to an S3 Bucket
To grant a Lambda function access to an S3 Bucket, we have to attach an IAM policy to the function's execution role.
The policy should grant permissions for all the Actions the function needs
to perform on the specified bucket.
For example, the following policy grants permission to upload objects to a specific S3 bucket.
YOUR_BUCKET placeholder with your bucket's name.{ "Version": "2012-10-17", "Statement": [ { "Effect": "Allow", "Action": [ "s3:PutObject", "s3:PutObjectAcl", "s3:GetObject", "s3:GetObjectAcl", "s3:AbortMultipartUpload" ], "Resource": [ "arn:aws:s3:::YOUR_BUCKET", "arn:aws:s3:::YOUR_BUCKET/*" ] } ] }
The permissions you have to grant your lambda function are use-case dependent.
"s3:*" for the Action element in the policy to grant full S3 access to the lambda function. However, it's best practice to grant an entity the least permissions that get the job done.You can view a full list of the S3 Actions by visiting
the docs.
There is a Description column that explains what each action does.
Most of the action names are intuitive, e.g. DeleteObject, GetObject,
PutObject, etc.
To attach a policy to the lambda function's execution role:
- Open the AWS Lambda console and click on your function's name.
- Click on the
Configurationtab and then clickPermissions.
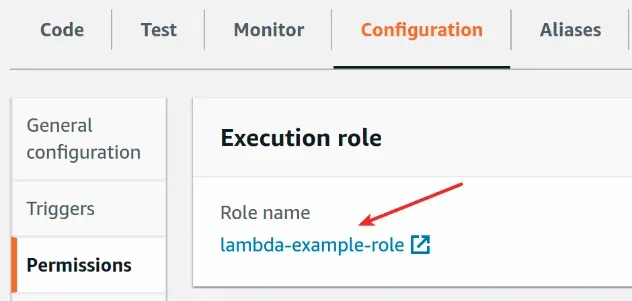
Click on the function's role.
Click on
Add Permissions, thenAttach policiesand click theCreate policybutton.In the JSON editor paste the following policy.
YOUR_BUCKET placeholder and adjust the Actions your lambda function needs to execute.{ "Version": "2012-10-17", "Statement": [ { "Effect": "Allow", "Action": [ "s3:Put*", "s3:Get*", "s3:Delete*" ], "Resource": [ "arn:aws:s3:::YOUR_BUCKET/*" ] } ] }
Click
Next: Tags, thenNext: Reviewand give your policy a name, then clickCreate policy.In the browser tab with the function's role, refresh the page to load the new policy and filter by the policy's name.
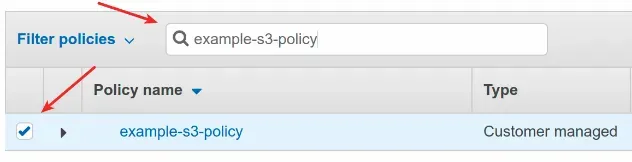
Click on the checkbox next to the policy and click
Attach Policies.
At this point, the lambda function's role has been extended with a policy that grants access to some S3 actions on a specific bucket.
Invoke your lambda function and verify whether it has access to the S3 bucket.
If your function is still unable to access S3, try to increase the function's
timeout by a second in the AWS console, or simply add an extra print
statement in the code and click the Deploy button.
If your Lambda function still doesn't have access to the S3 bucket, expand the IAM policy you added to the function's role and edit it to look like the policy below.
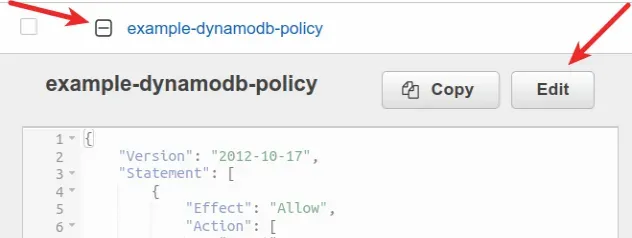
YOUR_BUCKET placeholder with the name of your S3 bucket.{ "Version": "2012-10-17", "Statement": [ { "Effect": "Allow", "Action": [ "s3:*" ], "Resource": [ "arn:aws:s3:::YOUR_BUCKET", "arn:aws:s3:::YOUR_BUCKET/*" ] } ] }
The IAM policy above grants full access to an S3 bucket, so your Lambda function will be able to execute all S3 actions on the bucket.
* symbol is useful when debugging.After you've updated the policy, try to invoke your Lambda function again. It should have permission to execute any action on the S3 bucket.
You can make the IAM policy less permissive after you verify which actions your lambda needs to run.
Deny effect will always override any Allow statements.I've also written a tutorial on how to add permissions to Lambda functions in AWS CDK.
# Grant a Lambda Function access to CloudWatch Logs
To grant a Lambda function permissions to log to CloudWatch, we have to attach
the AWSLambdaBasicExecutionRole AWS-managed policy to the function's execution
role.
The IAM policy grants permissions for the logs:CreateLogGroup,
logs:CreateLogStream and logs:PutLogEvents actions.
To attach the IAM policy to your Lambda function's role:
- Open the AWS Lambda console and click on your function's name.
- Click on the
Configurationtab and click onPermissionsin the sidebar.
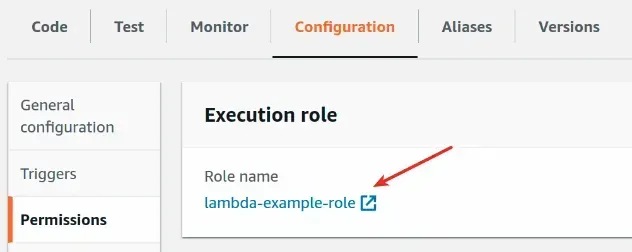
- Click on the role's name.
- In the
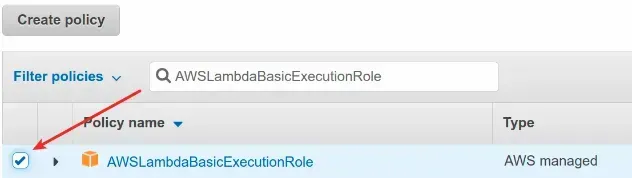
Permissionstab of the role, click onAdd permissionsandAttach policies. - Filter for
AWSLambdaBasicExecutionRolein the search input and click the checkbox next to the first result.
The AWSLambdaBasicExecutionRole managed policy contains the following
statement that allows our function to log to CloudWatch:
{ "Version": "2012-10-17", "Statement": [ { "Effect": "Allow", "Action": [ "logs:CreateLogGroup", "logs:CreateLogStream", "logs:PutLogEvents" ], "Resource": "*" } ] }
- Click on the
Attach policiesbutton
Invoke your lambda function to generate some logs.
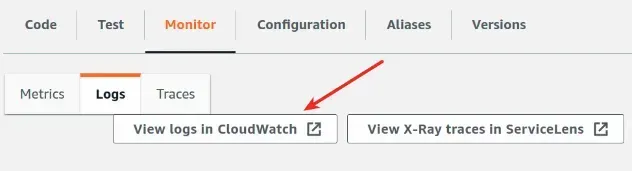
In the browser tab of the lambda function, click on the
Monitortab and selectView logs in CloudWatch.
- Click on the most recent log stream and you should see the logs of your Lambda function.
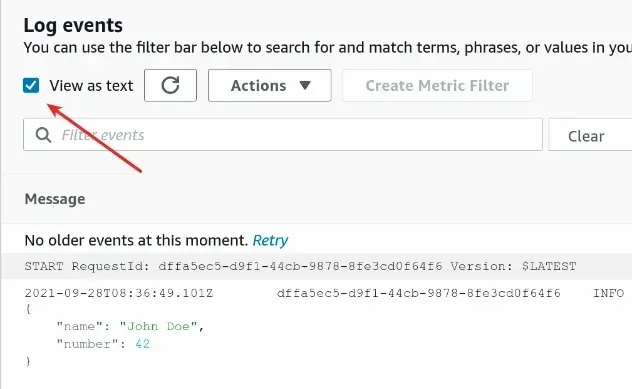
print statement in the function's code and click on the Deploy button.To get a better view of the logs, click on the View as text checkbox at the
top. It displays the logs as text, rather than a series of collapsible rows:
Note that AWS Lambda automatically creates a log group with the name
/aws/lambda/your-lambda-name as long as the function has the necessary
permissions.
I've also written a tutorial on how to add permissions to Lambda functions in AWS CDK.
# Additional Resources
You can learn more about the related topics by checking out the following tutorials:
- Grant AWS Lambda Access to Secrets Manager
- Grant AWS Lambda Access to an SQS Queue
- Grant AWS Lambda Access to a Dynamodb Table
- AWS CDK Tutorial for Beginners - Step-by-Step Guide
- How to use Parameters in AWS CDK
- Could not Parse Request body into JSON Error - AWS CLI
- Cannot find module (AWS Lambda Error) [Solved]
- S3 Access Denied when calling ListObjectsV2 error [Solved]
- S3 Access Denied when calling PutObject
- S3 Action does not Apply to any Resources Error
- The Bucket you are attempting to Access AWS S3 Error [Fixed]
- How to create a Cloudwatch Alarm in AWS CDK

